Irish cryptocurrency investors face a critical challenge: managing portfolios securely without surrendering control of their assets. Traditional credential sharing exposes accounts to theft and unauthorized access. Coinbase OAuth solves this by enabling secure, delegated access to third-party portfolio management tools without revealing passwords. This guide walks you through using Coinbase OAuth to connect trading platforms safely, maintain full asset control, and optimize your crypto investments while complying with Irish regulations. You’ll learn setup steps, security practices, and troubleshooting techniques to manage your portfolio confidently.
Table of Contents
- Understanding Coinbase OAuth And Its Benefits
- Preparing To Use Coinbase OAuth For Your Trading Needs
- Step-By-Step Guide To Connect And Trade Securely Using Coinbase OAuth
- Troubleshooting Common OAuth Issues And Ensuring Security Best Practices
- Manage Your Crypto Portfolio With CryptoCracker
- What Is Coinbase OAuth And How Does It Protect My Account?
Key takeaways
| Point | Details |
|---|---|
| OAuth2 security | Allows third-party apps to access your Coinbase account without sharing passwords, protecting credentials from theft. |
| Permission control | You authorize specific data and actions apps can perform, maintaining granular control over account access. |
| Irish compliance | Coinbase operates as a regulated VASP in Ireland, ensuring legal protections and anti-money laundering controls. |
| Token management | Proper setup and refresh of access tokens prevents trading errors and maintains seamless portfolio connections. |
| Best practices | Enabling 2FA, using least privilege permissions, and monitoring transactions safeguards your investments. |
Understanding Coinbase OAuth and its benefits
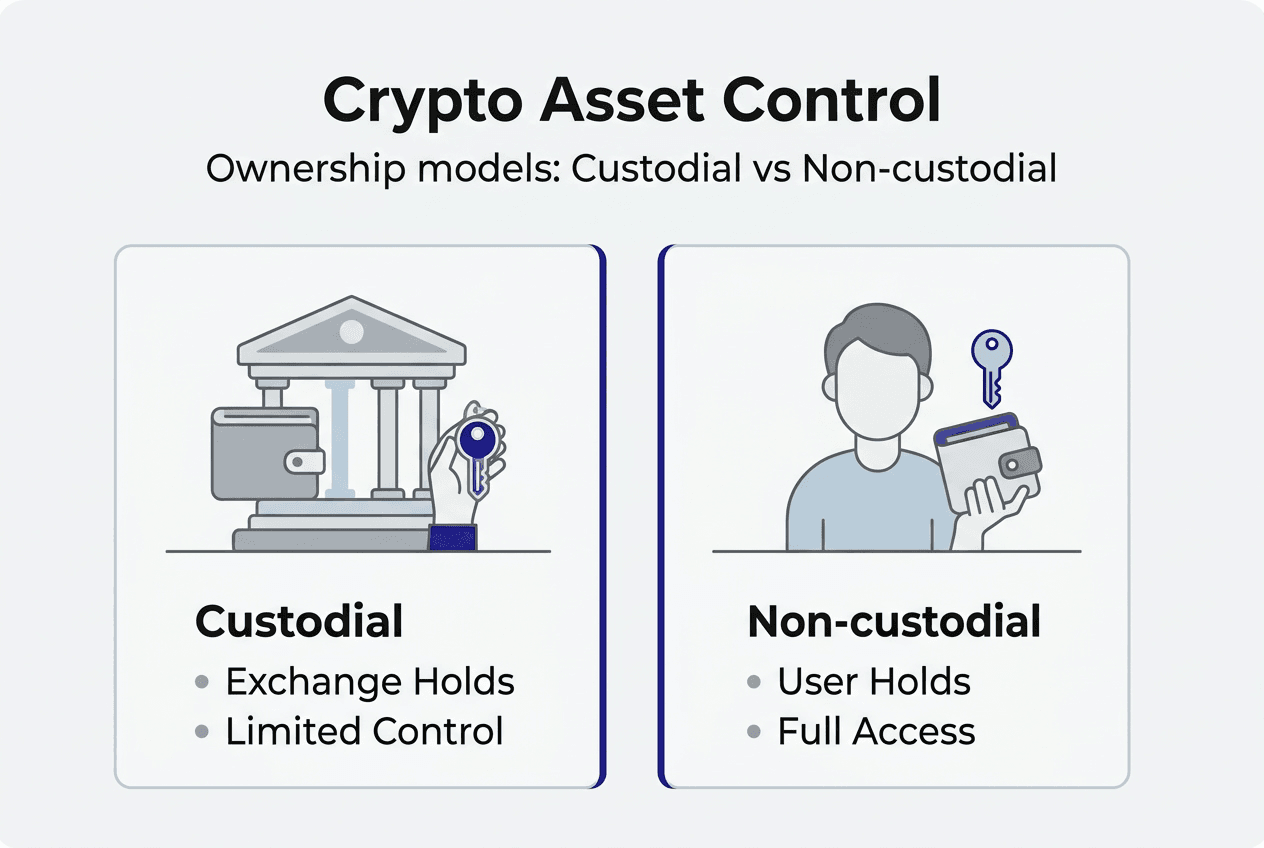
OAuth2 is an authorization framework that lets you grant third-party applications access to your Coinbase account without exposing your login credentials. When you connect a portfolio management tool, OAuth2 creates a secure channel where the app receives limited permissions you explicitly approve. This differs fundamentally from sharing usernames and passwords, which gives apps unrestricted control and leaves you vulnerable if the service is compromised.
The distinction between OAuth2 and API keys matters for portfolio management. OAuth2 handles user-facing applications that need account access on your behalf. API keys work for server-side automation where you control both the account and the application. For Irish investors using platforms like CryptoCracker to track multiple wallets and optimize trades, OAuth2 provides the right balance of functionality and security.
Key benefits include:
- Password protection: Your Coinbase credentials never leave the official login interface
- Granular permissions: You choose exactly what data and actions apps can access
- Token refresh: Access tokens expire and renew automatically, reducing long-term exposure
- Revocation control: You can disconnect apps instantly through your Coinbase settings
Non-custodial trading means you retain ownership and control of your cryptocurrency assets throughout the process. Unlike custodial exchanges that hold your funds, OAuth2 connections let portfolio tools view balances and execute trades while your assets stay in your Coinbase account. This model aligns with the preferences of Irish investors who prioritize asset security and regulatory compliance.
Pro Tip: Choose OAuth2 when connecting user-facing portfolio management apps that need to access your account data and execute trades on your behalf. Reserve API keys for server applications you personally control and operate.
The difference between Coinbase and Coinbase Wallet also impacts OAuth usage. Coinbase operates as a centralized exchange with OAuth support, while Coinbase Wallet functions as a self-custody solution requiring different connection methods. Understanding this distinction helps you select the right tools for your investment strategy.
Preparing to use Coinbase OAuth for your trading needs
Before connecting portfolio management tools through OAuth2, you need several prerequisites in place. A verified Coinbase account forms the foundation. If you plan to develop custom integrations or use specialized trading tools, registering a developer application on Coinbase’s platform becomes necessary. Understanding OAuth scopes determines what permissions your connected apps can request and receive.
Follow these setup steps:
- Create or verify your Coinbase account with complete identity documentation
- Enable two-factor authentication using an authenticator app for maximum security
- Register your application through Coinbase’s developer portal if building custom integrations
- Configure redirect URIs where Coinbase sends authorization codes after user approval
- Define required OAuth scopes matching your portfolio management needs
The OAuth Portfolio Access guide details available scopes for trading and account access. Common permissions include viewing wallet balances, reading transaction history, and placing buy or sell orders. Requesting only necessary scopes follows security best practices and builds user trust. Overly broad permissions raise red flags and increase risk if the connected application experiences a breach.
Coinbase’s approval as a VASP by Ireland’s Central Bank ensures your trading activities comply with local regulations. This regulatory framework provides legal protections, mandates anti-money laundering controls, and establishes clear operational standards. Irish investors benefit from these safeguards when using OAuth2 to connect portfolio tools.
Security preparations before connecting apps:
- Enable two-factor authentication on your Coinbase account
- Review and understand requested OAuth scopes before granting access
- Verify the legitimacy of third-party applications through reviews and documentation
- Set up transaction notifications to monitor account activity
- Document connected applications and their permission levels
The future of cryptocurrency in Ireland depends partly on investor adoption of secure practices like OAuth2. As regulatory frameworks mature, tools that prioritize user control and transparent permissions will dominate the market. Crypto management for Irish investors increasingly involves balancing convenience with security, making OAuth2 setup knowledge essential for portfolio optimization.
Step-by-step guide to connect and trade securely using Coinbase OAuth
The OAuth2 flow transforms authorization into a secure, multi-step process that protects your credentials while enabling portfolio management. Understanding each phase helps you troubleshoot issues and maintain continuous access to trading features.
Connection process:
- Click the connection button in your portfolio management application
- Get redirected to Coinbase’s official login page
- Enter your Coinbase credentials on the authentic Coinbase interface
- Review requested permissions and approve access for specific accounts
- Receive an authorization code sent to your application’s redirect URI
- Application exchanges the authorization code for access and refresh tokens
- Access token enables API calls to view balances and execute trades
The OAuth2 flow keeps your password isolated from third-party applications. When you log in, Coinbase validates your identity directly. The authorization code your app receives cannot access your account alone. It must be exchanged for tokens using credentials registered with Coinbase’s developer platform. This two-step verification prevents unauthorized access even if someone intercepts the authorization code.
Storing tokens securely is critical. Access tokens function like temporary keys to your account. Keep them encrypted in your application’s secure storage, never in plain text files or browser local storage. Refresh tokens enable obtaining new access tokens without repeated logins, but they carry even greater sensitivity. Treat them with the same protection level as passwords.
Using access tokens to call Coinbase’s Advanced Trade APIs unlocks portfolio management capabilities. You can retrieve real-time balance data, view transaction history, and place market or limit orders. Each API request includes your access token in the authorization header, proving your right to perform the action.
| Permission Type | OAuth2 Capability | API Key Capability |
|---|---|---|
| View balances | User account access | Own account only |
| Execute trades | User-authorized accounts | Own account only |
| Transaction history | User account access | Own account only |
| Account management | Granular user permissions | Full account control |
| Token refresh | Automatic renewal | Manual regeneration |
Pro Tip: Set up automatic token refresh in your portfolio application to maintain seamless access without repeated login prompts. Monitor refresh token expiration dates and implement renewal logic before they expire.
The permission error message “Target Account Not Tradable” appears when your OAuth token lacks access to specific accounts you’re trying to trade. This happens if you didn’t grant permission during initial authorization or if you have multiple portfolios with different access levels. Fix this by reauthorizing the application and explicitly granting access to all accounts you want to manage.
Getting started with cryptocurrency trading in Ireland becomes simpler when you understand OAuth2 mechanics. The technology removes technical barriers while maintaining security standards that protect your investments. Irish investors can focus on portfolio strategy rather than credential management.
Troubleshooting common OAuth issues and ensuring security best practices
Even with proper setup, OAuth2 connections occasionally encounter errors that disrupt portfolio management. Recognizing common issues and their solutions keeps your trading tools functioning smoothly.
Frequent OAuth errors and causes:
- Invalid token: Access token expired and needs refresh using the refresh token
- Insufficient permissions: OAuth scope doesn’t include the requested action or account
- Wrong redirect URI: Application configuration doesn’t match registered redirect URLs
- Revoked access: User manually disconnected the application through Coinbase settings
- Rate limiting: Too many API requests in a short timeframe triggering throttling
OAuth2 security best practices form the foundation of safe portfolio management. Enable two-factor authentication on your Coinbase account before connecting any applications. This adds a verification layer even if someone obtains your password. Use authenticator apps rather than SMS for stronger protection against SIM swapping attacks.
Apply least privilege principles when granting OAuth permissions. Only authorize the specific scopes your portfolio tool needs to function. If an application requests broad permissions beyond its stated purpose, question whether you should connect it. Review connected applications quarterly through your Coinbase security settings and revoke access to tools you no longer use.
API vulnerabilities like Broken Object Level Authorization highlight why strict validation matters. The BOLA vulnerability demonstrates how improper access controls let attackers manipulate requests to access unauthorized accounts. While Coinbase implements protections, you must verify that connected applications follow secure development practices.
Securely storing OAuth tokens protects against unauthorized access. Never commit tokens to version control systems or share them in support requests. Use encrypted storage solutions and rotate tokens periodically. If you suspect token compromise, immediately revoke access through Coinbase and reauthorize with new credentials.
Monitoring transactions detects unauthorized activity early. Set up email or push notifications for all trades and withdrawals. Review your transaction history weekly to identify unfamiliar activity. If you spot suspicious trades, revoke OAuth access immediately and contact Coinbase support. Quick response limits potential losses and helps trace the security breach.
Regularly reviewing app permissions maintains control over your portfolio access. As your investment strategy evolves, the tools you need may change. Disconnect applications you no longer use to reduce your attack surface. When connecting new tools, verify their security practices and read user reviews about data handling.
The role of regulation and compliance in digital assets extends to OAuth implementations. Irish regulations require transparent data handling and user consent mechanisms. Applications serving Irish investors must comply with GDPR and financial regulations. Verify that your portfolio management tools provide clear privacy policies and data protection measures.
Manage your crypto portfolio with CryptoCracker
Secure OAuth connections unlock powerful portfolio management when paired with the right platform. CryptoCracker simplifies tracking multiple wallets and optimizing trades through Coinbase integration. Our platform uses OAuth2 to access your portfolio data securely, providing real-time insights without storing your credentials.

CryptoCracker features for Irish investors:
- Portfolio tracking across multiple exchanges and wallets in one dashboard
- Trade optimization tools that analyze market conditions and suggest entry points
- Security alerts for unusual account activity or permission changes
- Tax reporting assistance aligned with Irish cryptocurrency regulations
- Auto-savings functionality to build positions during market dips
Pro Tip: Use CryptoCracker’s trade recommendation tool alongside Coinbase OAuth to identify optimal trading opportunities while maintaining full control of your assets through secure, non-custodial connections.
How CryptoCracker optimizes your portfolio through data-driven analysis and automated suggestions. Our platform connects to your Coinbase account via OAuth, analyzes performance trends, and provides actionable recommendations. You maintain complete asset control while benefiting from institutional-grade analytics.
Explore our guide to cryptocurrency wallets to understand how different storage solutions integrate with portfolio management tools. Combining secure OAuth connections with comprehensive tracking transforms how Irish investors manage and grow their crypto holdings.
What is Coinbase OAuth and how does it protect my account?
Coinbase OAuth allows third-party portfolio management applications to access your account without requiring your password. You authorize specific permissions through Coinbase’s official interface, and the application receives temporary access tokens. This separation protects your credentials from exposure to external services. If a connected application experiences a security breach, your Coinbase password remains safe and you can revoke access instantly.
How do I prevent permission errors like “Target Account Not Tradable”?
Ensure your OAuth token includes permissions for both cryptocurrency and fiat accounts you want to trade. During the authorization process, explicitly grant access to all relevant portfolios. If errors persist after initial setup, disconnect and reauthorize the application through your Coinbase security settings. Review the requested OAuth scopes to confirm they match your intended trading activities.
Is Coinbase regulated in Ireland and how does that affect me?
Coinbase operates as an approved VASP in Ireland under Central Bank supervision, ensuring compliance with local financial regulations. This regulatory status provides legal protections, mandates anti-money laundering controls, and establishes clear operational standards. Irish investors benefit from increased transparency, dispute resolution mechanisms, and confidence that their trading activities meet regulatory requirements. The future of cryptocurrency in Ireland depends on such regulatory frameworks building trust.
Can I use Coinbase OAuth if I am not tech-savvy?
Coinbase OAuth requires minimal technical knowledge from users. The authorization flow uses familiar login interfaces you already know from accessing your Coinbase account. You simply click connect in your portfolio management app, log into Coinbase normally, and approve the requested permissions. Connected applications handle token exchanges and API calls behind the scenes. Clear instructions from reputable platforms like CryptoCracker guide you through each step, making secure portfolio management accessible regardless of technical expertise.