Many investors believe cryptocurrency is inherently secure because of blockchain technology. This misconception leads to complacency and preventable losses. While blockchain provides a robust foundation, security breaches remain a leading cause of financial devastation in crypto markets. Your assets are only as safe as the practices and tools you implement. This guide reveals how security impacts every investment decision you make and provides actionable strategies to protect your portfolio in 2026. Understanding these principles transforms you from a vulnerable trader into a confident, security-conscious investor.
Table of Contents
- Why Security Is Paramount In Cryptocurrency Investing
- Core Security Technologies Protecting Your Crypto Assets
- Regulation, Compliance, And Their Roles In Crypto Security
- Best Practices And Tools For Securing Your Crypto Portfolio In 2026
- Enhance Your Crypto Security With CryptoCracker Tools
Key takeaways
| Point | Details |
|---|---|
| Security protects assets | Robust security measures prevent theft, fraud, and irreversible losses in cryptocurrency investments. |
| Wallet knowledge matters | Understanding hardware, software, and cold storage options significantly enhances your asset protection. |
| Compliance reduces risk | Regulatory frameworks and compliance standards promote transparency and investor trust in digital markets. |
| Habits minimize vulnerabilities | Consistent security practices like MFA and regular audits protect against evolving threats. |
| Tools optimize protection | Leveraging specialized platforms and security software strengthens portfolio defense mechanisms. |
Why security is paramount in cryptocurrency investing
Cryptocurrency exists purely in digital form, making it a prime target for cybercriminals. Unlike traditional banking systems with insurance protections and fraud reversal mechanisms, crypto transactions are typically irreversible. Once your assets leave your wallet through unauthorized access, recovery becomes nearly impossible. This fundamental characteristic makes security the single most critical factor in successful crypto investing.
The decentralized nature of cryptocurrency markets creates both opportunities and vulnerabilities. Without central authorities monitoring transactions or reversing fraudulent activity, you bear complete responsibility for protecting your holdings. Demystifying crypto investment requires accepting this reality and implementing appropriate safeguards.
Investor negligence accounts for a substantial portion of crypto losses. Weak passwords, shared private keys, and inadequate wallet protection create easy entry points for attackers. Phishing schemes targeting crypto holders have become increasingly sophisticated, tricking even experienced investors into revealing sensitive information. Your security posture directly determines whether you maintain control of your investments or become another statistic.
Several factors make crypto security uniquely challenging:
- Digital assets lack physical presence, making theft invisible until discovered
- Private keys represent single points of failure for entire portfolios
- Exchange vulnerabilities expose multiple users simultaneously
- Regulatory gaps leave investors with limited legal recourse
- Anonymous transactions make tracking stolen funds extremely difficult
Trust forms the foundation of long-term crypto market viability. When major security breaches occur, market confidence erodes and prices typically decline. Your individual security practices contribute to the broader ecosystem’s stability. Strong security habits protect not only your portfolio but also strengthen the entire crypto community’s resilience against threats.
Core security technologies protecting your crypto assets
Encryption serves as the backbone of cryptocurrency security. This mathematical process converts readable data into coded information that only authorized parties can decrypt. When you send crypto transactions, encryption methods secure the transfer and verify authenticity. Understanding basic encryption principles helps you evaluate wallet security and make informed decisions about asset storage.
Wallet selection dramatically impacts your security profile. Hardware wallets store private keys on physical devices isolated from internet connections, providing maximum protection against remote attacks. Software wallets offer convenience for frequent transactions but maintain constant internet connectivity, increasing exposure to potential breaches. Hot wallets facilitate quick trading while cold wallets prioritize long-term storage security. Each type serves specific purposes in a balanced security strategy.

| Wallet Type | Security Level | Convenience | Best Use Case |
|---|---|---|---|
| Hardware | Highest | Low | Long-term holdings |
| Software (Desktop) | Medium | Medium | Regular trading |
| Mobile | Medium | High | Small transactions |
| Web | Lower | Highest | Minimal holdings |
| Paper | High | Lowest | Backup storage |
Blockchain technology provides inherent security through distributed ledger systems. Every transaction gets recorded across thousands of nodes, making unauthorized alterations virtually impossible. However, this network security does not automatically protect individual user accounts. You must implement proper key management practices to benefit from blockchain’s protective features.
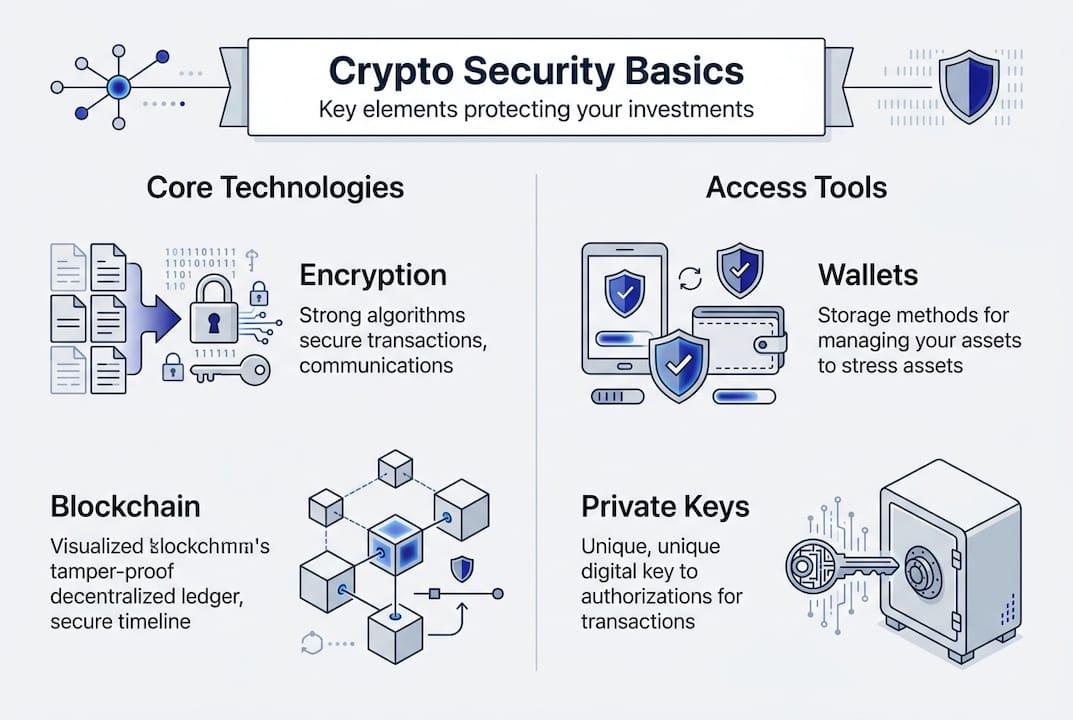
Private keys and seed phrases represent your ultimate access credentials. These cryptographic codes prove ownership and authorize transactions. Losing your private key means permanent loss of access, while exposing it grants complete control to anyone who obtains it. Never store keys digitally on internet-connected devices or share them with any service claiming to need access. Write seed phrases on durable materials and store them in secure physical locations.
Pro Tip: Enable automatic updates for all wallet software and applications. Security patches address newly discovered vulnerabilities, and delayed updates leave your assets exposed to known exploits that attackers actively target.
Multi-signature wallets require multiple private keys to authorize transactions, distributing control and reducing single points of failure. This approach works exceptionally well for business accounts or shared holdings where multiple parties should approve significant movements. The cryptocurrency wallets guide explains implementation strategies for various security models.
Regulation, compliance, and their roles in crypto security
Regulatory frameworks have matured significantly in 2026, providing clearer guidelines for exchanges, investors, and service providers. These rules establish minimum security standards, require transparency in operations, and create accountability mechanisms. While regulation cannot eliminate all risks, it substantially reduces fraud and provides legal recourse when violations occur. Regulation and compliance are vital for building sustainable crypto markets.
Know Your Customer (KYC) and Anti-Money Laundering (AML) policies require exchanges to verify user identities. Critics argue these measures compromise privacy, but they significantly reduce criminal activity and protect legitimate investors. When exchanges implement robust KYC processes, they create barriers against money laundering, terrorist financing, and fraud schemes. This verification also enables authorities to investigate theft and potentially recover stolen assets.
Compliance standards protect investors through several mechanisms:
- Mandatory security audits identify vulnerabilities before exploitation
- Insurance requirements provide compensation for certain breach scenarios
- Reporting obligations increase transparency and early threat detection
- Licensing processes eliminate unqualified or malicious operators
- Consumer protection rules establish clear rights and responsibilities
European Union regulations, including MiCA (Markets in Crypto-Assets), set comprehensive standards for crypto service providers. These rules mandate specific security measures, capital requirements, and operational procedures. Platforms operating under these frameworks typically offer greater protection than unregulated alternatives. Understanding which regulations apply to your chosen exchanges helps you assess their reliability.
The evolving nature of crypto regulation and compliance creates both opportunities and challenges. New rules sometimes impose restrictions that limit certain trading strategies or increase operational costs. However, regulatory clarity attracts institutional investors and mainstream adoption, ultimately strengthening market stability. Staying informed about regulatory changes helps you adapt your security practices and maintain compliance.
Transparency requirements force exchanges to disclose security practices, audit results, and incident responses. This information empowers you to make educated decisions about where to trade and store assets. Platforms that resist transparency often hide inadequate security measures or questionable business practices. Prioritize exchanges that voluntarily exceed minimum regulatory requirements and openly communicate their security posture.
Best practices and tools for securing your crypto portfolio in 2026
Implementing a comprehensive security routine protects your investments from the majority of common threats. Start by securing your private keys using hardware wallets for significant holdings and encrypted storage for backup copies. Never photograph seed phrases or store them in cloud services, email, or messaging apps. Physical security for these credentials matters as much as digital protection.
- Generate unique, complex passwords for every crypto-related account using a reputable password manager
- Enable Multi-Factor Authentication (MFA) on all exchanges, wallets, and related services
- Use authenticator apps rather than SMS-based verification, which remains vulnerable to SIM swapping attacks
- Regularly review account activity and transaction history for unauthorized access attempts
- Maintain separate email addresses dedicated exclusively to crypto accounts
- Update all software, applications, and firmware immediately when patches become available
- Verify website URLs carefully before entering credentials to avoid phishing sites
- Test wallet recovery processes with small amounts before trusting them with significant holdings
Multi-Factor Authentication adds critical protection layers beyond passwords. Authenticator apps generate time-based codes that expire quickly, making stolen credentials useless without physical device access. Hardware security keys provide even stronger protection by requiring physical possession for authentication. The minor inconvenience of MFA pales compared to the devastating consequences of compromised accounts.
Regular portfolio monitoring detects suspicious activity before major damage occurs. Set up alerts for transactions, login attempts, and balance changes. Review these notifications promptly and investigate anything unexpected. Many security breaches get discovered days or weeks after initial compromise, giving attackers extended access to drain accounts gradually. Understanding security impact on transaction integrity helps you recognize warning signs early.
| Security Tool | Primary Function | Cost Range | Recommended For |
|---|---|---|---|
| Ledger Nano X | Hardware wallet | $150-200 | Serious investors |
| YubiKey | Hardware MFA | $45-70 | All users |
| 1Password | Password management | $36/year | Everyone |
| CryptoCracker | Portfolio monitoring | Variable | Active traders |
Pro Tip: Automate security features like trailing stop-losses and price alerts through platforms that support these functions. Automated protections respond instantly to market movements or suspicious activity, providing defense even when you cannot actively monitor your portfolio.
The secure wallet transfer guide explains proper procedures for moving assets between storage solutions. Always send test transactions with minimal amounts before transferring significant holdings. Verify receiving addresses character by character, as malware can modify clipboard contents to redirect transfers. Understanding these technical details prevents costly mistakes that compromise security.
Portfolio diversification across multiple wallets and exchanges reduces concentration risk. If one platform experiences a breach, your entire portfolio does not become compromised. However, managing multiple accounts increases complexity and potential for errors. Balance security benefits against practical management capabilities. Tools like portfolio optimization with CryptoCracker help coordinate multi-platform strategies while maintaining security standards.
Regular security audits of your own practices identify weaknesses before attackers exploit them. Review which services have access to your accounts, update recovery information, and verify backup procedures remain functional. Security is not a one-time setup but an ongoing commitment that adapts to evolving threats. Scheduling quarterly reviews ensures your defenses remain current and effective.
Enhance your crypto security with CryptoCracker tools
CryptoCracker provides comprehensive security-focused features designed specifically for investors prioritizing asset protection. Our platform integrates cryptocurrency wallets guide principles with real-time monitoring capabilities that alert you to suspicious activity instantly. We understand that security and profitability are inseparable in successful crypto investing.

Our portfolio optimization with CryptoCracker tools incorporate security metrics alongside performance indicators. This holistic approach helps you make informed decisions that balance growth potential with risk management. Automated features reduce human error while maintaining the control you need over your investments. The platform’s EU regulatory compliance ensures we meet rigorous security standards that protect your data and assets. Visit CryptoCracker platform to explore how our tools can strengthen your security posture while optimizing returns.
FAQ
How do hardware wallets improve crypto security?
Hardware wallets store private keys on physical devices that never connect directly to the internet, eliminating remote hacking risks. They require physical possession and PIN authentication to authorize transactions, creating multiple security layers. Even if your computer contains malware, attackers cannot access keys stored on hardware wallets. The cryptocurrency wallets guide provides detailed comparisons of leading hardware wallet options.
What are the biggest security risks for crypto investors in 2026?
Phishing attacks, exchange hacks, poor private key management, and social engineering schemes represent primary threats. Sophisticated phishing sites perfectly mimic legitimate platforms, tricking users into revealing credentials. Exchange vulnerabilities continue despite improved security, making diversified storage essential. User awareness and updated security tools effectively mitigate most threats when implemented consistently.
How can regulation affect my crypto security?
Regulation enforces minimum security standards for exchanges and service providers, reducing fraud and increasing accountability. Licensed platforms must maintain insurance, conduct regular audits, and implement specific protective measures. However, crypto regulation and compliance frameworks remain evolving and cannot eliminate all risks. You still bear primary responsibility for securing your assets regardless of regulatory protections.
Should I use hot or cold wallets for my crypto holdings?
Use cold wallets for long-term holdings you do not trade frequently, as they provide maximum security through offline storage. Hot wallets suit active trading and regular transactions where convenience matters more than absolute security. Most investors benefit from combining both approaches, keeping the majority of assets in cold storage while maintaining smaller amounts in hot wallets for immediate access. Your specific needs determine the optimal balance.
How often should I update my crypto security practices?
Review and update security practices quarterly at minimum, or immediately when major vulnerabilities or breaches occur in the crypto ecosystem. Technology and threat landscapes evolve rapidly, requiring adaptive security strategies. Schedule regular audits of passwords, MFA settings, authorized devices, and backup procedures. Staying current with security developments through trusted sources helps you anticipate and prevent emerging threats before they impact your portfolio.