TL;DR:
- Over $3.7 billion in crypto losses result from transaction vulnerabilities, not just market volatility.
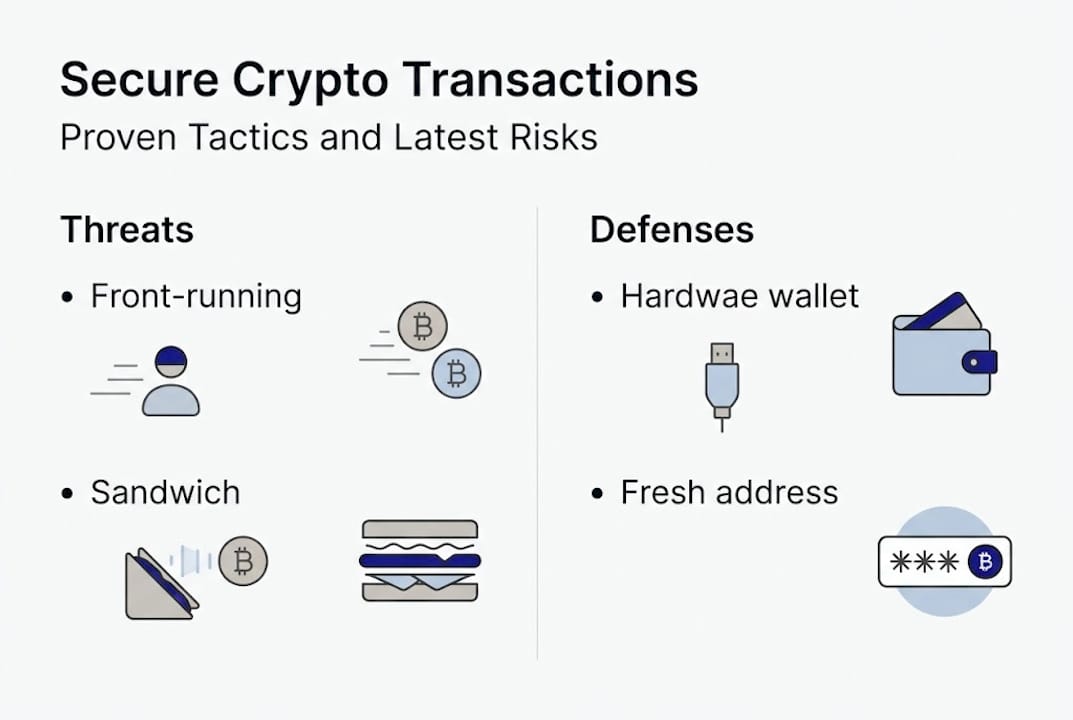
- Recognizing attack types like front-running and sandwich attacks helps protect your transactions.
- Privacy best practices and continuous behavioral discipline are essential for long-term crypto security.
Many investors believe the biggest risk to their crypto is market volatility. That assumption leaves a much quieter threat wide open. Over $3.7B in crypto thefts could be prevented with basic security practices, yet the losses keep coming. The problem usually isn’t the wallet balance itself. It’s the transaction, the moment your funds move from one address to another. That’s where attackers focus, and that’s exactly where most users leave the door cracked open. This guide breaks down the real threats targeting your transactions today and gives you a clear, actionable roadmap to close those gaps before they cost you.
Table of Contents
- The landscape of crypto transaction vulnerabilities
- Why transaction privacy is essential to security
- Core best practices for secure crypto transactions
- Emerging threats and advanced countermeasures
- Why most crypto security guides fail investors — and what actually keeps assets safe
- Enhance your crypto security with the right tools
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Threats are dynamic | Crypto transaction risks are constantly evolving with new attack types emerging monthly. |
| Privacy enhances safety | Breaking transaction linkages and using privacy tools significantly boosts security. |
| Layered defenses work best | Combining hardware wallets, address hygiene, and vigilant software updates offers robust protection. |
| User habits are critical | Even the best technology is undermined by neglecting regular checks or repeating old mistakes. |
The landscape of crypto transaction vulnerabilities
Before you can defend something, you need to understand what’s attacking it. Crypto transactions face a wide range of threats that go far beyond simple hacking. Many of these attacks exploit the very transparency and speed that make blockchains useful.
Here are the key attack types every investor should recognize:
Front-running: An attacker spots your pending transaction in the mempool (the waiting area before confirmation) and submits their own transaction with a higher fee to jump ahead of yours, profiting from the price movement your trade will cause.
Sandwich attacks: A more aggressive version of front-running. The attacker places one transaction before yours and one after, squeezing your trade between theirs to extract profit at your expense.
Race attacks: A malicious actor broadcasts two conflicting transactions simultaneously, trying to get an unconfirmed payment accepted before the network catches the double-spend.
Transaction malleability: Exploits a flaw in how transaction IDs are generated, allowing attackers to alter a transaction’s ID without changing its content, which can cause accounting confusion on exchanges.
Replay attacks: When a blockchain forks, a transaction valid on one chain can sometimes be “replayed” on the other, draining funds without the user’s knowledge.
Common vulnerabilities include front-running, sandwich attacks, race attacks, and protocol-specific flaws, and all of them are actively exploited today.
| Attack type | Blockchains primarily affected | Notable recent losses |
|---|---|---|
| Sandwich attacks | Ethereum, Solana | $500M+ on Solana (16 months) |
| Front-running | Ethereum, BSC | Hundreds of millions annually |
| Race attacks | Bitcoin, Ethereum | Tens of millions per year |
| Replay attacks | Any forked chain | Varies by event |
| Transaction malleability | Bitcoin (legacy) | Historical exchange losses |
Sandwich attacks on Solana and Ethereum have caused major losses, with over $500M extracted from Solana users alone across just 16 months. That’s not a hypothetical risk. It’s an active drain on real portfolios.
Red flags that a transaction may be at risk:
- Unusual slippage or price impact warnings on DEX trades
- Pending transactions stuck in the mempool for extended periods
- Unexpected fee spikes during a trade
- Receiving less than expected on a swap without a clear explanation
- Wallet software that hasn’t been updated in months
Awareness is step one. Once you can recognize these patterns, you’re already better protected than the majority of crypto users. We encourage you to explore secure transaction methods to build on this foundation.
Why transaction privacy is essential to security
Blockchains are public by design. Every transaction you make is recorded permanently on a ledger that anyone can read. That transparency is a feature, but it’s also a vulnerability. When your wallet addresses can be linked together, attackers, data brokers, and even thieves can build a detailed picture of your holdings and behavior.

Privacy enhances security by decoupling identity from transaction history, breaking the chain of information that makes targeted attacks possible. If no one can connect your addresses to each other or to your identity, your exposure shrinks dramatically.
Here’s a direct comparison of basic versus advanced privacy tactics:
| Tactic | Basic approach | Advanced approach | Chain analysis risk |
|---|---|---|---|
| Address use | Reuse same address | Fresh address per transaction | High vs. Low |
| Transaction mixing | None | CoinJoin or similar tools | High vs. Moderate |
| Wallet structure | Single wallet for all | Segregated wallets by purpose | High vs. Low |
| Network exposure | Standard node connection | Own node or privacy relay | Moderate vs. Low |
Simple privacy steps that strengthen your transaction security:
- Generate a new receiving address for every single transaction
- Separate your KYC-linked wallets from your personal and cold wallets
- Avoid posting wallet addresses publicly on social media or forums
- Use a privacy-focused wallet that supports CoinJoin or similar protocols
- Limit on-chain activity to what’s necessary, reducing your traceable footprint
Pro Tip: Most wallets allow you to generate fresh addresses automatically. Make this a habit, not an afterthought. The less your addresses cluster together, the harder you are to track and target. You can learn more about privacy in crypto trading and why it matters more than most guides admit.
Core best practices for secure crypto transactions
Knowing the threats is only half the equation. Acting on that knowledge is where protection actually happens. Whether you’re new to crypto or a seasoned trader, there’s a tiered approach that works for every level.
Novice-friendly practices:
- Always send a small test transaction before moving large amounts to a new address.
- Double-check the recipient address character by character, never just the first and last few digits.
- Use a hardware wallet for long-term storage rather than keeping funds on an exchange.
- Keep your wallet software and firmware updated consistently.
- Enable two-factor authentication on every platform you use.
Advanced user practices:
- Run your own full node to verify transactions independently, without trusting a third party.
- Use coin control features to manage which UTXOs (unspent transaction outputs) are included in each transaction.
- Stay informed about MEV (Maximal Extractable Value) risks and use MEV-protected relays when transacting on Ethereum.
- Sign transactions offline using air-gapped hardware for maximum security.
- Review PSBT (Partially Signed Bitcoin Transaction) details carefully before finalizing.
“Security is not a product you buy once. It’s a practice you maintain continuously. A layered approach, combining hardware protection, behavioral discipline, and protocol awareness, is the only realistic defense against today’s evolving threats.”
Best practices include hardware wallets, offline signing, address verification, and CoinJoin as a core foundation. These aren’t optional extras. They’re the baseline.
Pro Tip: Never use a single wallet for everything. Maintain at least three: one for KYC-linked activity, one for personal transactions, and one cold wallet for long-term storage. This simple separation limits the blast radius if one wallet is ever compromised.
We’ve put together detailed resources on crypto security best practices and expert strategies for crypto investors that go deeper on each of these points. Our crypto wallet guide is a solid next step if you want to sharpen your wallet setup, and for a full overview, maximize your crypto security with our dedicated security resource.
Emerging threats and advanced countermeasures
Best practices serve as the foundation, but proactive adaptation is crucial as attackers keep innovating. The threat landscape in 2026 includes attack types that didn’t exist just a few years ago, and staying ahead means knowing what’s coming before it hits.
Protocol vulnerabilities like Phantom Signature (CVE-2025-29774), BRC20 snipping, and new variants require vigilance because they target the signing and verification layer of transactions, an area most users never think to question. BRC20 snipping exploits the ordering of inscriptions on Bitcoin to steal assets. Signature forgery attacks manipulate how transactions are validated. Long-range attacks target proof-of-stake chains by rewriting history from a much earlier block.
Proactive defenses every serious investor should consider:
- Run your own node to independently verify blocks and transactions without relying on third-party RPC endpoints
- Use MEV-protected relays such as Flashbots Protect for Ethereum transactions to reduce sandwich attack exposure
- Subscribe to security bulletins from wallet providers and blockchain developers so you learn about vulnerabilities before attackers exploit them
- Audit any DeFi protocols or smart contracts you interact with using third-party security reviews
- Test wallet signing behavior after any firmware or software update, especially major version changes
Sandwich attacks on Ethereum have waned but persist, and MEV and sandwich risks remain a real concern even as protocol-level fixes are debated.
“Fixes at the user level still matter enormously because protocols evolve slowly. Waiting for the network to solve everything is a strategy that consistently costs people money.”
The threat landscape changes monthly. Staying informed isn’t paranoia. It’s the minimum standard for anyone serious about protecting their assets. Explore security in crypto investing to keep your knowledge current as conditions evolve.
Why most crypto security guides fail investors — and what actually keeps assets safe
We read a lot of security guides, and most of them share the same blind spot. They focus almost entirely on technology: the right hardware wallet, the right protocol, the right software. What they miss is that the vast majority of real losses come from predictable, repeatable human mistakes.
It only takes one moment. One address reused out of convenience. One transaction signed on a public WiFi network. One software update ignored for a month. That’s the real attack surface, and no hardware wallet in the world protects against it.
The investors who stay protected aren’t just using better tools. They think differently. They review their setup regularly, not once and then forget it. They treat every unusual prompt or unexpected fee as a potential red flag rather than an inconvenience to click through. They build skepticism into their workflow.
Pro Tip: Spend five minutes thinking like an attacker. Look at your own setup and ask: what’s the easiest way to steal from me right now? That exercise reveals weak points faster than any checklist.
Layered defenses, regular reviews, and a healthy distrust of “set-and-forget” solutions are what separate the truly protected from those who just feel protected. We think tools and strategies for safer crypto should always be paired with that mindset shift, not used as a substitute for it.
Enhance your crypto security with the right tools
Understanding threats and best practices is a powerful start. Putting that knowledge into practice with the right platform makes it sustainable.

At CryptoCracker, we’ve built our platform specifically to support secure, informed crypto management. From real-time portfolio monitoring to API-integrated transaction tracking via Coinbase, our tools are designed to give you visibility without adding complexity. Our wallet and monitoring guide is a great place to start, and our features for optimizing your crypto portfolio help you stay on top of performance and risk in one place. If you’re comparing options, see how CryptoCracker stacks up as one of the leading crypto manager alternatives available today.
Frequently asked questions
What is the most common way crypto transactions are compromised?
Front-running, sandwich attacks, and address reuse are the most common vectors, exposing transaction details and enabling attackers to profit from or intercept your funds before confirmation.
Are hardware wallets enough to keep my crypto safe?
Hardware wallets reduce risk significantly, but full protection requires combining them with address hygiene, privacy tools, and consistent software updates.
How can I avoid privacy leaks when transacting crypto?
Generate a fresh address for each transaction, never reuse addresses, and consider tools like CoinJoin, which breaks transaction linkage and makes chain analysis much harder.
What are sandwich attacks and how do I protect against them?
Sandwich attacks exploit mempool visibility to front-run and back-run your trade for profit. Use MEV-aware tools and private relays to significantly reduce your exposure.
Why do losses keep occurring even as security improves?
New attack variants emerge constantly and user habits lag behind, making ongoing education, tool updates, and behavioral discipline the only reliable long-term defense.